Contents
- 1 Essential Trust Wallet Security Fundamentals
- 2 Recovery Phrase Protection Best Practices
- 3 Recognizing and Avoiding Trust Wallet Phishing Attacks
- 4 Secure DApp Browser and Web3 Interaction
- 5 Device Security and Access Control
- 6 Multi-Chain Security Considerations
- 7 Safe Trading and Staking Practices
- 8 Advanced Security Features and Settings
- 9 Conclusion
- 10 Frequently Asked Questions
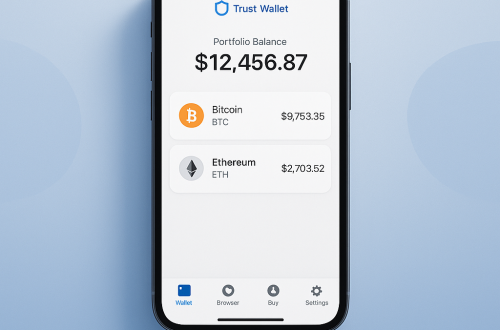
Securing your cryptocurrency is one of the most critical aspects of your Web3 journey. With the growing adoption of digital assets and DeFi protocols, protecting your funds has never been more important. Trust Wallet, the self-custodial mobile crypto wallet backed by Binance, provides robust security features while maintaining the simplicity that millions of users worldwide rely on.
As a non-custodial wallet, Trust Wallet puts you in complete control of your private keys and recovery phrase. This empowerment comes with responsibility – understanding how to protect Trust Wallet and avoid scams Trust Wallet users might encounter is essential for safe crypto management. Whether you’re new to cryptocurrency or an experienced DeFi user managing NFTs across multiple blockchains, implementing proper security practices ensures your digital assets remain safe.
In this comprehensive guide, you’ll discover essential Trust Wallet security tips, learn how to recognize and avoid phishing attempts, understand secure crypto practices, and master the tools that keep your multi-chain wallet protected. Let’s explore how to maximize your security while enjoying seamless access to Web3, DeFi, and the broader cryptocurrency ecosystem.
Essential Trust Wallet Security Fundamentals
Trust Wallet’s security foundation relies on industry-standard encryption and self-custodial architecture. Unlike custodial exchanges, your private keys never leave your device, and Trust Wallet never stores your recovery phrase on external servers. This design ensures that only you have access to your cryptocurrency, NFTs, and DeFi positions across 100+ supported blockchains.
The wallet employs multiple security layers, including biometric authentication, PIN protection, and secure enclave storage on supported devices. When you create a Trust Wallet, a unique 12-word recovery phrase is generated using cryptographically secure randomization. This recovery phrase serves as the master key to all your crypto assets and can restore your entire wallet on any device.
Understanding these fundamentals helps you make informed decisions about securing your digital assets. Trust Wallet’s open-source nature means the code is publicly auditable, providing transparency that’s often missing from centralized solutions. This combination of self-custody, transparency, and robust encryption creates a strong foundation for cryptocurrency security.
Recovery Phrase Protection Best Practices
Your 12-word recovery phrase is the most critical element of Trust Wallet security. Anyone with access to this phrase can completely control your wallet and all associated funds across every blockchain. Proper recovery phrase management is essential for long-term security and peace of mind.
Never store your recovery phrase digitally in emails, cloud storage, photos, or text files. Physical storage using paper or metal backup cards provides the highest security. Write clearly and double-check each word’s spelling – even small errors can prevent wallet recovery. Consider creating multiple physical copies and storing them in different secure locations.
- Write recovery phrase on paper or engrave on metal
- Store copies in multiple secure, private locations
- Never take photos or save digitally
- Verify word order and spelling multiple times
- Never share with anyone, including support staff
- Consider using a safety deposit box for long-term storage
Remember that Trust Wallet support will never ask for your recovery phrase. Any request for these words is a scam attempt. Legitimate troubleshooting never requires sharing your private keys or recovery phrase.
Recognizing and Avoiding Trust Wallet Phishing Attacks
Trust Wallet phishing attempts have become increasingly sophisticated as cryptocurrency adoption grows. Scammers create fake websites, apps, and support channels that closely mimic official Trust Wallet branding. Understanding common phishing tactics helps protect your wallet from unauthorized access.
Always download Trust Wallet exclusively from official sources: Apple App Store, Google Play Store, or the official Trust Wallet website. Fake apps in unofficial stores often contain malware designed to steal your recovery phrase. Similarly, only visit trustwallet.com for official information – check the URL carefully as scammers create similar-looking domains.
Phishing attempts often arrive via email, social media, or messaging apps claiming urgent security issues or promising rewards. These messages typically include links to fake websites that capture your recovery phrase when entered. Trust Wallet never sends unsolicited emails requesting sensitive information or offering cryptocurrency giveaways.
- Bookmark the official Trust Wallet website (trustwallet.com)
- Verify app authenticity before downloading
- Ignore unsolicited emails or messages about your wallet
- Never enter your recovery phrase on websites
- Check URLs carefully for spelling variations
- Use official Trust Wallet social media channels for support
Secure DApp Browser and Web3 Interaction
Trust Wallet’s built-in DApp browser enables direct interaction with decentralized applications, DeFi protocols, and NFT marketplaces. While this provides convenient access to Web3 services, it also requires additional security awareness when connecting to smart contracts and signing transactions.
Before connecting to any DApp, research the protocol thoroughly and verify you’re accessing the official website. Many DeFi exploits occur through fake DApps that drain connected wallets. Always review transaction details carefully before signing, including gas fees, token permissions, and contract interactions.
Use WalletConnect for additional security when possible, as it creates encrypted connections between Trust Wallet and DApps without exposing your private keys. This protocol enables secure interaction with DeFi platforms while maintaining your wallet’s security integrity.
Consider using a separate wallet with limited funds for experimental DeFi interactions. This approach, often called a “hot wallet,” minimizes potential losses if you encounter malicious smart contracts while keeping your main holdings secure in cold storage or a more protected wallet.
Device Security and Access Control
Your mobile device security directly impacts Trust Wallet protection. Enable device-level security features including screen locks, biometric authentication, and automatic updates. These measures create additional barriers against unauthorized wallet access if your phone is lost or stolen.
Trust Wallet supports biometric authentication on compatible devices, adding convenience without compromising security. Fingerprint or face recognition provides quick access while ensuring others cannot easily open your wallet. Combine biometric protection with a strong PIN as backup authentication.
Avoid using Trust Wallet on jailbroken or rooted devices, as these modifications can compromise built-in security features. Similarly, be cautious when installing apps from unknown sources or granting unnecessary permissions that might access your wallet data.
Regular security audits of your device help maintain optimal protection. Review installed apps, remove unnecessary software, and ensure your operating system receives timely security updates. Consider using dedicated devices for cryptocurrency management if you hold significant value.
Multi-Chain Security Considerations
Trust Wallet’s support for over 10 million tokens across 100+ blockchains requires understanding chain-specific security considerations. Each blockchain has unique characteristics, transaction fees, and potential vulnerabilities that affect your overall security posture.
When managing assets across multiple chains, pay attention to bridge security and cross-chain transaction verification. Blockchain bridges can be targets for exploits, so research bridge protocols thoroughly and consider the risks of moving large amounts between chains.
Different blockchains have varying confirmation times and finality guarantees. Ethereum transactions provide strong finality but may have higher fees, while faster chains might require more confirmations for equivalent security. Understanding these trade-offs helps you make informed decisions about asset storage and transfers.
Monitor your multi-chain portfolio regularly using Trust Wallet’s unified interface. Unusual activity on any supported blockchain could indicate security issues requiring immediate attention. Set up price alerts and transaction notifications to stay informed about your holdings across all chains.
Safe Trading and Staking Practices
Trust Wallet’s integrated trading and staking features provide convenient access to earning opportunities, but they require careful security consideration. When using the built-in swap function or participating in staking programs, always verify transaction details and understand the associated risks.
For crypto swaps, compare rates across multiple platforms to ensure fair pricing and avoid potential scams. Trust Wallet aggregates liquidity from various sources, but always review slippage tolerance and transaction fees before confirming trades. Large trades may benefit from splitting across multiple smaller transactions to reduce market impact.
In-app staking through Trust Wallet provides exposure to various proof-of-stake networks, but understand the lock-up periods and unstaking requirements for each protocol. Staked assets typically cannot be immediately withdrawn, so only stake funds you won’t need for the specified duration.
- Verify staking terms and lock-up periods
- Research validator reputation and performance
- Understand slashing risks for each network
- Monitor staking rewards and performance regularly
- Diversify across multiple validators when possible
- Keep some assets liquid for immediate needs
Advanced Security Features and Settings
Trust Wallet offers several advanced security settings that enhance protection for experienced users. Transaction signing preferences, custom networks, and privacy settings provide granular control over your wallet’s behavior and security profile.
Enable transaction confirmation prompts for all operations, including small transfers. While this adds an extra step, it prevents accidental transactions and provides opportunities to review details before confirming. This feature is particularly valuable when interacting with new DApps or smart contracts.
Custom network settings allow interaction with testnets and alternative blockchain implementations, but exercise caution when adding unknown networks. Malicious network configurations can redirect transactions or expose sensitive information. Only add networks from trusted sources and verify configuration details.
Privacy settings control how Trust Wallet handles analytics and data sharing. Review these preferences periodically to ensure they align with your privacy expectations. While some data helps improve the application, you can opt out of non-essential tracking.
Conclusion
Implementing comprehensive Trust Wallet security tips creates a robust foundation for safe cryptocurrency management. From protecting your recovery phrase and avoiding phishing scams to securing DApp interactions and multi-chain transactions, each security layer contributes to your overall protection. The combination of Trust Wallet’s self-custodial architecture and your security practices ensures complete control over your digital assets.
Remember that security is an ongoing process, not a one-time setup. Regularly review your practices, stay informed about new threats, and keep your Trust Wallet app updated with the latest security improvements. The Web3 ecosystem continues evolving, and maintaining strong security habits protects your ability to safely explore DeFi, NFTs, and emerging cryptocurrency opportunities.
Your journey into decentralized finance and Web3 applications becomes more confident with proper security foundations. Trust Wallet provides the tools and features necessary for safe crypto management – implementing these security tips ensures you can fully enjoy the benefits of self-custodial cryptocurrency storage while minimizing risks.
Ready to enhance your cryptocurrency security? Download Trust Wallet today and start implementing these security best practices to protect your digital assets across all supported blockchains and DeFi protocols.
Frequently Asked Questions
Is Trust Wallet safe to use?
Yes, Trust Wallet is a secure self-custodial wallet that uses industry-standard encryption. Your private keys remain on your device, and Trust Wallet never stores your recovery phrase on external servers. The wallet is open-source and backed by Binance, providing transparency and institutional support.
What should I do if I lose my recovery phrase?
Unfortunately, if you lose your recovery phrase, there’s no way to recover your wallet or access your funds. Trust Wallet cannot reset or recover your recovery phrase since it’s never stored on external servers. This emphasizes the importance of securely storing multiple copies of your recovery phrase in different locations.
How can I tell if a Trust Wallet app is legitimate?
Only download Trust Wallet from official sources: Apple App Store, Google Play Store, or trustwallet.com. Verify the developer is “Six Days LLC” and check user reviews. Fake apps often have poor ratings, limited reviews, or slightly different names. Never download Trust Wallet from third-party websites or unofficial app stores.
Should I share my Trust Wallet recovery phrase with support?
Never share your recovery phrase with anyone, including Trust Wallet support. Legitimate support never requires your recovery phrase, private keys, or PIN. Any request for these credentials is a scam attempt. Trust Wallet support can help with app issues without accessing your wallet directly.
How do I protect myself from DApp scams?
Research DApps thoroughly before connecting your wallet. Verify official websites through trusted sources, read smart contract audits, and start with small amounts for testing. Always review transaction details before signing, and be suspicious of unusually high returns or urgent investment opportunities.
Can someone hack Trust Wallet remotely?
Trust Wallet’s self-custodial design means your private keys are stored locally on your device, making remote hacking extremely difficult. However, phishing attacks, malware, or device theft can compromise security. Following proper security practices and keeping your device secure protects against these threats.
What’s the difference between Trust Wallet and exchange wallets?
Trust Wallet is self-custodial, meaning you control your private keys and recovery phrase. Exchange wallets are custodial – the exchange controls your keys. While exchanges offer convenience and customer support, self-custodial wallets like Trust Wallet provide complete ownership and control over your cryptocurrency.
How often should I backup my Trust Wallet?
Your recovery phrase never changes, so you only need to back it up once securely. However, regularly verify that your backup is readable and stored safely. If you create additional wallets within Trust Wallet, each has its own recovery phrase that must be backed up separately.
Is it safe to use Trust Wallet on public WiFi?
While Trust Wallet uses encrypted connections, public WiFi networks can pose security risks. Avoid conducting large transactions or accessing sensitive DApps on public networks. If necessary, use a VPN for additional protection and avoid entering your recovery phrase on any network you don’t fully trust.
What should I do if I suspect my Trust Wallet is compromised?
Immediately transfer all assets to a new wallet with a fresh recovery phrase. Create the new wallet on a clean device and never reuse the potentially compromised recovery phrase. Monitor your old wallet for any unauthorized transactions and report suspicious activity to relevant authorities if necessary.
Can I use Trust Wallet for business cryptocurrency management?
Trust Wallet works for business use, but consider multi-signature solutions for enhanced security with business funds. Implement strict recovery phrase management protocols and consider using separate wallets for different business functions. For large amounts, hardware wallet integration provides additional security layers.
How do I verify Trust Wallet transaction authenticity?
All Trust Wallet transactions are recorded on their respective blockchains and can be verified using blockchain explorers. Copy transaction hashes from your wallet history and search them on explorers like Etherscan (Ethereum), BscScan (BSC), or appropriate explorers for other chains. This provides independent confirmation of transaction details.




Straight to the point, the focus on Web3 features. This is exactly what beginners need. Author did a great job explaining clearly. Great resource. Thanks again! Thanks again! Highly recommend. Great resource.
Well-structured material. great breakdown of user interface. Very practical approach. Really appreciate this guide. Great resource. Well done! Thanks again! Great resource. Thanks again! Well done! Great resource.
Solid information, especially about NFT gallery. Wasn’t aware of these nuances before. Very helpful and practical. Highly recommend. Well done! Highly recommend. Well done! Very helpful! Well done! Highly recommend.
Perfect timing, those wanting to understand crypto security better. Well explained. Info came in very handy. Great resource. Well done! Thanks again! Great resource. Great resource. Thanks again! Well done!
Just what I needed, the FAQ section was especially helpful and informative. Information is truly up-to-date. Thanks again! Highly recommend. Well done! Highly recommend. Well done! Highly recommend. Highly recommend.
Exactly what I was looking for, particularly useful insights on multi-chain support and DApp browser. Info came in very handy. Highly recommend. Well done! Well done! Great resource. Great resource. Highly recommend.
Excellent article, the getting started section was especially helpful and informative. Really appreciate this guide. Great resource. Great resource. Great resource. Highly recommend. Highly recommend.
Just what I needed, especially about NFT gallery. Wasn’t aware of these nuances before. Perfect resource for this topic. Very helpful! Well done! Well done! Great resource. Highly recommend. Well done!
Quality overview, the explanation of user interface. Made everything much clearer. Great work by the author! Very helpful! Very helpful! Great resource. Highly recommend. Well done! Well done! Thanks again!
Very useful information, particularly useful insights on NFT gallery and NFT management. Information is truly up-to-date. Well done! Highly recommend. Highly recommend. Great resource. Great resource.
Just what I needed, exactly the information I needed about multi-chain support. Really appreciate this guide. Thanks again! Very helpful! Well done! Very helpful! Well done! Highly recommend. Well done!
Quality overview, the DeFi guide section was especially helpful and informative. Thanks for the detailed explanation! Great resource. Thanks again! Thanks again! Well done! Very helpful! Highly recommend.
Comprehensive guide, really helped me understand NFT management. Now I know how to manage my crypto. Everything explained clearly. Well done! Highly recommend. Very helpful! Great resource. Very helpful!